To ensure high credibility of the cryptographic operations it is necessary to utilize specialized certified HW devices, which are optimized for secure generation and storage of keys for critical crypto operations.
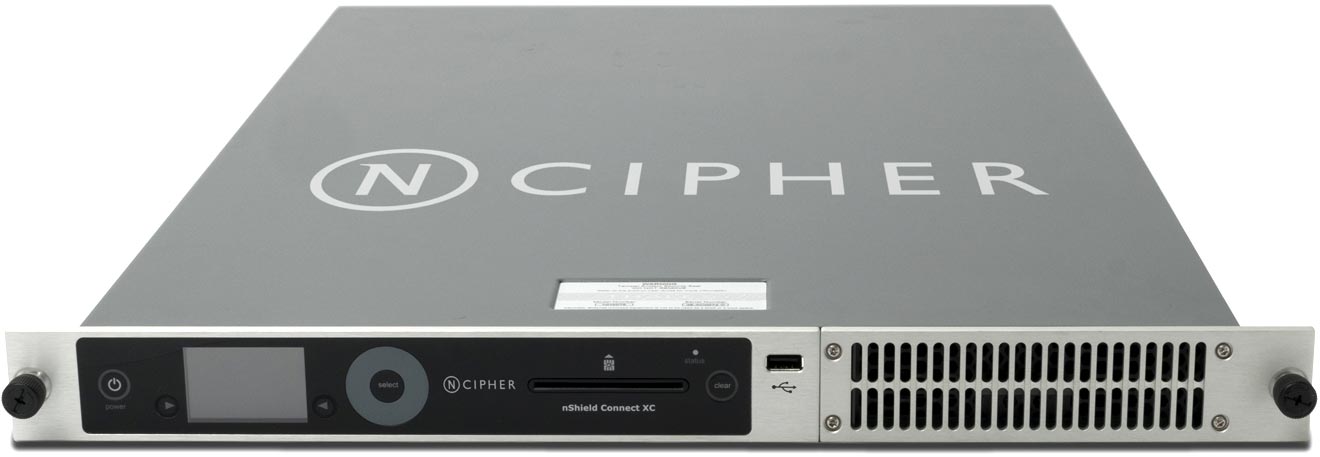
From the perspective of the public key infrastructure the most effective and user-friendly devices are the hardware security modules (HSM). These devices bear specific means of security, which in case of HSM theft make the access to protected operations impossible. The devices support standard algorithms with various key lengths, and standard APIs for integration. HSM may be used in following scenarios:
Qualified signature creation device (QSignCD)
Qualified seal creation device (QSealCD)
Secure device for generation and storage of the private key for internal certification authority and/or data encryption, etc.
SEFIRA has realized several projects regarding implementation of HSM for remote signature, qualified sealing and internal certification authorities.